Unlocking the Secrets of UV Keys: A Comprehensive Guide to Applications, Technology, and Future Trends
In today’s technologically advanced world, the concept of security and authentication has evolved significantly. Among the various methods developed, UV keys stand out as a sophisticated and increasingly popular solution. This comprehensive guide delves into the intricacies of UV keys, exploring their applications, underlying technology, benefits, limitations, and future trends. Whether you’re a security professional, a technology enthusiast, or simply curious about the latest advancements in authentication, this article provides a detailed overview of UV keys and their role in modern security systems.
What are UV Keys?
UV keys, short for Ultraviolet Keys, are authentication devices that utilize ultraviolet (UV) light to verify identity or grant access. These keys often incorporate a unique pattern or code that is visible only under UV light. When the key is exposed to a UV light source, the hidden pattern becomes visible, allowing a sensor or camera to read and verify the key’s authenticity. This method adds an extra layer of security, making it significantly harder to duplicate or counterfeit compared to traditional keys or simple electronic access cards.
UV keys are not just limited to physical keys; the concept has expanded to digital applications as well. In digital security, a UV key could refer to a digital signature or watermark embedded into an image or document, which is only detectable under UV analysis. This ensures the integrity and authenticity of the digital content, preventing unauthorized modifications or reproductions.
The Technology Behind UV Keys
The technology behind UV keys is multifaceted, involving materials science, optics, and electronics. Several key components work together to make UV keys effective:
1. UV-Sensitive Materials
The core of a UV key lies in the materials that react to ultraviolet light. These materials, often phosphorescent or fluorescent compounds, absorb UV light and re-emit it at a different wavelength, making the hidden pattern visible. The choice of material is crucial as it determines the intensity and color of the emitted light, which in turn affects the accuracy of the detection system.
2. UV Light Sources
A reliable UV light source is essential for activating the UV key. These sources can range from simple UV LEDs to more powerful UV lamps, depending on the application. The wavelength of the UV light must be carefully chosen to match the absorption spectrum of the UV-sensitive material. Additionally, the intensity of the light source must be sufficient to produce a clear and detectable pattern.
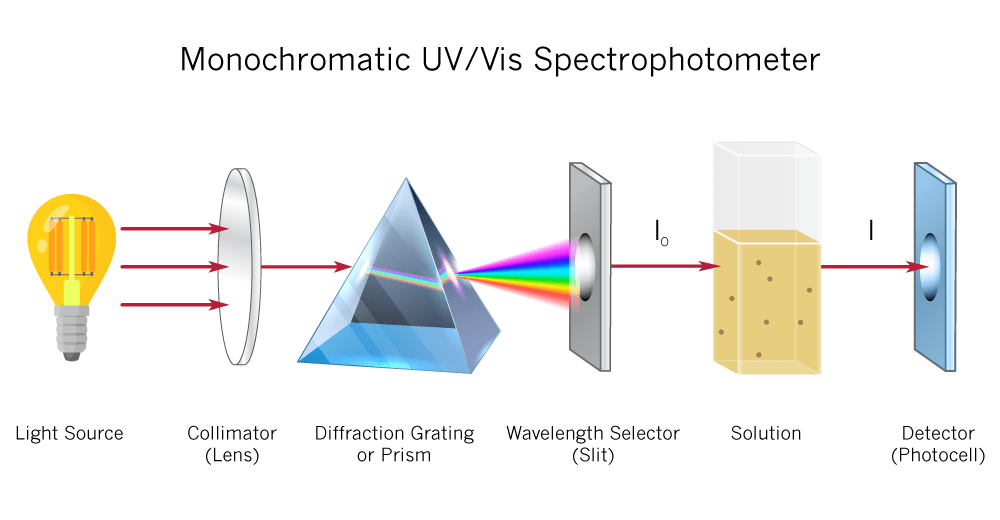
3. Detection Systems
The detection system is responsible for capturing and interpreting the UV-induced pattern. This typically involves a camera or sensor that is sensitive to the emitted light. The system may also include filters to block out ambient light and enhance the contrast of the UV pattern. Advanced detection systems can even analyze the spectral characteristics of the emitted light to further verify the key’s authenticity.
4. Encryption and Encoding
In many applications, the UV pattern is not simply a static image but an encoded message. This message can contain information about the key’s owner, the access rights granted, or other relevant data. Encryption techniques are often used to protect this information from unauthorized access or modification. The encoding scheme must be robust and resistant to tampering to ensure the security of the UV key.
Applications of UV Keys
UV keys have a wide range of applications across various industries. Their unique security features make them suitable for scenarios where authentication and anti-counterfeiting are critical.
1. Physical Security
In physical security, UV keys can be used to control access to buildings, rooms, or equipment. Traditional locks and keys are vulnerable to picking and duplication, while electronic access cards can be easily cloned. UV keys offer a higher level of security by incorporating a hidden UV pattern that is difficult to replicate. This makes them ideal for high-security environments such as government facilities, research labs, and data centers.
2. Brand Protection
Counterfeiting is a major problem for many brands, leading to significant financial losses and damage to reputation. UV keys can be used to authenticate products and packaging, making it easier for consumers and authorities to identify genuine items. For example, a UV watermark can be added to pharmaceutical packaging, luxury goods, or currency to prevent counterfeiting. This not only protects the brand but also ensures the safety and quality of the products.
3. Document Authentication
Important documents such as passports, identity cards, and certificates are often targets for forgery. UV keys can be used to add an extra layer of security to these documents, making them more difficult to counterfeit. A UV pattern can be embedded into the document during the printing process, which is only visible under UV light. This allows authorities to quickly verify the authenticity of the document and prevent fraudulent use.
4. Digital Security
In the digital realm, UV keys can be used to protect digital content from unauthorized copying and distribution. A UV watermark can be embedded into images, videos, or documents, which is only detectable using specialized software. This allows content creators to track and control the usage of their work and prevent copyright infringement. UV keys can also be used to authenticate digital signatures and ensure the integrity of electronic transactions.
5. Supply Chain Management
UV keys can play a crucial role in supply chain management by tracking and authenticating goods as they move through the supply chain. A UV tag can be attached to products or containers, which is scanned at various checkpoints to verify the product’s origin and authenticity. This helps to prevent the entry of counterfeit goods into the supply chain and ensures that products meet the required quality standards.
Benefits of Using UV Keys
UV keys offer several advantages over traditional security methods, making them an attractive option for various applications.
1. Enhanced Security
The primary benefit of UV keys is their enhanced security. The use of UV light to verify identity adds an extra layer of protection that is difficult to bypass. Unlike traditional keys or access cards, UV keys cannot be easily duplicated or cloned, making them more resistant to theft and fraud.
2. Versatility
UV keys are versatile and can be adapted to a wide range of applications. They can be used in physical security, brand protection, document authentication, digital security, and supply chain management. This versatility makes them a valuable tool for organizations looking to improve their security posture.
3. Cost-Effectiveness
While the initial investment in UV key technology may be higher than traditional methods, the long-term cost-effectiveness can be significant. UV keys reduce the risk of theft, fraud, and counterfeiting, which can result in substantial financial losses. Additionally, the durability and reliability of UV keys can reduce maintenance and replacement costs.
4. Ease of Use
UV keys are generally easy to use, both for end-users and administrators. The verification process is typically quick and straightforward, requiring only a UV light source and a detection system. Administrators can easily manage UV keys and track their usage, providing valuable insights into security performance.
5. Scalability
UV key systems can be easily scaled to accommodate growing security needs. Whether it’s adding more users, expanding the range of applications, or integrating with other security systems, UV keys can be adapted to meet the evolving requirements of an organization.
Limitations of UV Keys
Despite their many benefits, UV keys also have some limitations that should be considered.
1. Dependence on UV Light
UV keys rely on a UV light source to function. If the light source fails or is unavailable, the key cannot be verified. This dependence can be a problem in situations where power is unreliable or where UV light sources are not readily accessible.
2. Vulnerability to Sophisticated Attacks
While UV keys are more secure than traditional methods, they are not immune to sophisticated attacks. Determined attackers may be able to replicate the UV pattern using advanced imaging techniques or by synthesizing UV-sensitive materials. Therefore, it’s essential to implement additional security measures to protect against these types of attacks.
3. Environmental Factors
The performance of UV keys can be affected by environmental factors such as temperature, humidity, and exposure to sunlight. These factors can degrade the UV-sensitive materials and reduce the visibility of the UV pattern. It’s important to choose materials that are resistant to these environmental factors and to protect UV keys from harsh conditions.
4. Cost of Implementation
The initial cost of implementing a UV key system can be higher than traditional methods. This includes the cost of UV keys, UV light sources, detection systems, and software. However, the long-term cost-effectiveness of UV keys can outweigh the initial investment.
Future Trends in UV Key Technology
UV key technology is constantly evolving, with new advancements being developed to improve security, reliability, and ease of use. Some of the key trends in UV key technology include:
1. Integration with Biometrics
Combining UV keys with biometric authentication methods such as fingerprint scanning or facial recognition can provide an even higher level of security. This multi-factor authentication approach makes it much more difficult for attackers to bypass the security system.
2. Miniaturization
Advances in materials science and microelectronics are leading to the miniaturization of UV key technology. This allows UV keys to be integrated into smaller devices such as smartphones, wearables, and IoT devices.
3. Advanced Encryption
The use of advanced encryption techniques to protect the data encoded in the UV pattern is becoming increasingly common. This ensures that even if the UV pattern is compromised, the underlying data remains secure.
4. AI-Powered Detection Systems
Artificial intelligence (AI) is being used to develop more sophisticated detection systems that can analyze the UV pattern with greater accuracy and speed. These AI-powered systems can also detect subtle variations in the UV pattern that may indicate tampering or counterfeiting.
5. Self-Verifying UV Keys
Researchers are developing self-verifying UV keys that can automatically detect and report any tampering or damage. These keys would be equipped with sensors that monitor the integrity of the UV pattern and alert the user or administrator if any issues are detected.
Conclusion
UV keys represent a significant advancement in security and authentication technology. Their ability to incorporate hidden patterns visible only under ultraviolet light provides a robust defense against counterfeiting and unauthorized access. While they are not without limitations, the benefits of enhanced security, versatility, and cost-effectiveness make them an attractive option for a wide range of applications. As technology continues to evolve, we can expect to see even more innovative uses of UV keys in the future, further solidifying their role in modern security systems. From physical security to digital authentication, UV keys are poised to play a crucial role in protecting our assets and identities in an increasingly complex world.
The ongoing advancements in materials science, optics, and electronics will undoubtedly lead to more sophisticated and reliable UV key systems. Integration with biometrics, AI-powered detection systems, and self-verifying capabilities will further enhance the security and usability of UV keys. As organizations continue to prioritize security and authentication, UV keys will remain a valuable tool for protecting against fraud, theft, and unauthorized access. Whether you’re a security professional, a technology enthusiast, or simply someone who values privacy and security, understanding the principles and applications of UV keys is essential in today’s digital age.
