Understanding MPLS Traffic: A Comprehensive Guide
MPLS, or Multiprotocol Label Switching, is a crucial data forwarding technology used in modern networks. Understanding MPLS traffic and its management is essential for network engineers and administrators to ensure optimal network performance, reliability, and security. This comprehensive guide delves into the intricacies of MPLS traffic, exploring its underlying principles, applications, and management techniques.
What is MPLS?
MPLS is a data forwarding technique that uses labels to direct data packets through a network. Instead of relying on complex IP address lookups at each hop, MPLS assigns short labels to packets, allowing routers to quickly forward traffic based on these labels. This significantly speeds up the forwarding process, making MPLS ideal for high-performance networks.
The key difference between traditional IP routing and MPLS is the forwarding decision process. In IP routing, each router analyzes the destination IP address of a packet to determine the next hop. This process is repeated at every router along the path. In contrast, MPLS performs the routing decision only once at the ingress router, where a label is assigned to the packet. Subsequent routers simply forward the packet based on the label, reducing processing overhead and improving efficiency.
How MPLS Works
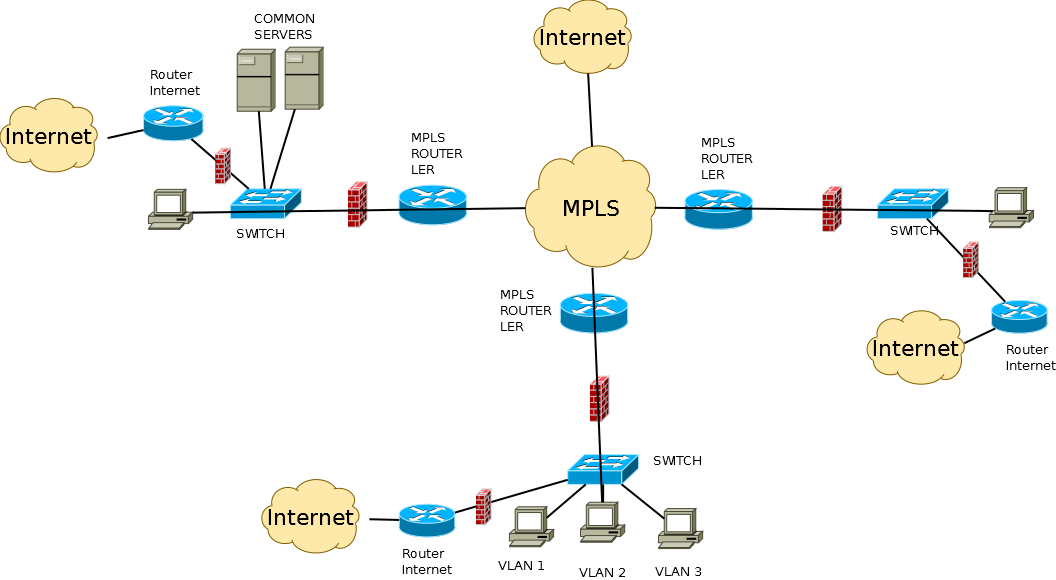
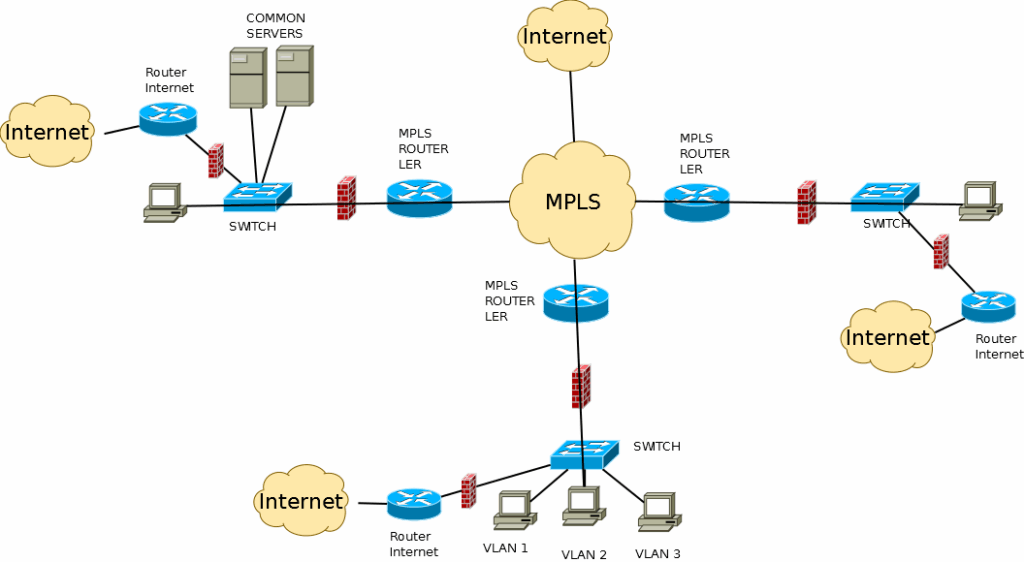
MPLS operates using several key components:
- Label Switched Path (LSP): The path that MPLS traffic takes through the network. It’s established based on routing protocols and traffic engineering policies.
- Label Switching Router (LSR): Routers that forward packets based on MPLS labels. They are the core components of an MPLS network.
- Ingress LSR: The first LSR in an LSP. It assigns the initial label to incoming packets.
- Egress LSR: The last LSR in an LSP. It removes the MPLS label before forwarding the packet to its final destination.
The process begins when a packet enters the MPLS network at the ingress LSR. The ingress LSR analyzes the packet’s destination IP address and applies an appropriate MPLS label. This label is then added to the packet header. As the packet traverses the LSP, each LSR examines the label and forwards the packet to the next hop based on its label forwarding table. The egress LSR removes the label before delivering the packet to its destination. This streamlined forwarding process significantly reduces latency and improves network performance.
Benefits of MPLS
MPLS offers several key benefits that make it a popular choice for modern networks:
- Improved Performance: By using labels for forwarding, MPLS reduces the processing overhead on routers, resulting in faster packet forwarding and lower latency.
- Traffic Engineering: MPLS allows network administrators to control the path that MPLS traffic takes through the network, enabling them to optimize network utilization and avoid congestion.
- Quality of Service (QoS): MPLS supports QoS mechanisms, allowing administrators to prioritize certain types of MPLS traffic, such as voice and video, to ensure a better user experience.
- VPN Support: MPLS is commonly used to create Virtual Private Networks (VPNs), providing secure and isolated communication between different sites.
- Scalability: MPLS can be scaled to support large and complex networks, making it suitable for both enterprise and service provider environments.
MPLS Traffic Engineering
One of the most significant advantages of MPLS is its ability to perform traffic engineering. Traffic engineering allows network administrators to control the path that MPLS traffic takes through the network, enabling them to optimize network utilization and avoid congestion. This is achieved by creating explicit LSPs that bypass congested links or utilize underutilized paths. [See also: MPLS Network Design Best Practices]
MPLS traffic engineering can be used to:
- Balance network load: Distribute MPLS traffic evenly across the network to prevent congestion on specific links.
- Improve network resilience: Create backup LSPs that can be used in case of link failures.
- Optimize network performance: Route MPLS traffic along paths with the lowest latency or highest bandwidth.
Implementing effective MPLS traffic engineering strategies requires careful planning and monitoring. Network administrators need to analyze MPLS traffic patterns, identify potential bottlenecks, and configure LSPs accordingly. Regular monitoring and adjustments are necessary to ensure that the network continues to operate efficiently.
Monitoring MPLS Traffic
Monitoring MPLS traffic is crucial for maintaining network performance and identifying potential issues. Network administrators need to monitor various metrics, such as MPLS traffic volume, latency, and packet loss, to ensure that the network is operating within acceptable parameters. Several tools and techniques can be used to monitor MPLS traffic:
- NetFlow/sFlow: These protocols collect MPLS traffic flow data and provide insights into network usage patterns.
- SNMP: Simple Network Management Protocol (SNMP) can be used to monitor the status of MPLS devices and interfaces.
- MPLS Ping and Traceroute: These tools can be used to test the connectivity and performance of MPLS LSPs.
- Network Performance Monitoring (NPM) tools: These tools provide comprehensive visibility into network performance, including MPLS traffic analysis.
By actively monitoring MPLS traffic, network administrators can proactively identify and resolve issues before they impact users. This helps to ensure a stable and reliable network environment. Early detection of anomalies within MPLS traffic is key to preventing larger network outages. [See also: Best Practices for Network Monitoring]
Securing MPLS Traffic
Securing MPLS traffic is essential to protect sensitive data and prevent unauthorized access. While MPLS itself does not provide inherent security mechanisms, several techniques can be used to enhance the security of MPLS traffic:
- Encryption: Encrypting MPLS traffic using protocols like IPsec can protect data from eavesdropping.
- Access Control Lists (ACLs): ACLs can be used to filter MPLS traffic based on source and destination addresses, ports, and other criteria.
- Firewalls: Firewalls can be deployed at the edge of the MPLS network to protect against external threats.
- Intrusion Detection and Prevention Systems (IDPS): IDPS can be used to detect and prevent malicious activity on the MPLS network.
It’s important to implement a layered security approach to protect MPLS traffic. This involves combining multiple security mechanisms to provide comprehensive protection. Regular security audits and vulnerability assessments are also essential to identify and address potential weaknesses. Properly securing MPLS traffic ensures the confidentiality, integrity, and availability of critical network resources.
MPLS Applications
MPLS is used in a wide range of applications, including:
- VPNs: MPLS is commonly used to create VPNs, providing secure and isolated communication between different sites.
- Voice over IP (VoIP): MPLS can be used to prioritize VoIP MPLS traffic, ensuring high-quality voice communication.
- Video conferencing: MPLS can be used to optimize video conferencing MPLS traffic, providing a smooth and seamless user experience.
- Cloud computing: MPLS can be used to connect enterprises to cloud service providers, providing secure and reliable access to cloud resources.
- Data center interconnect: MPLS can be used to connect data centers, enabling seamless data replication and disaster recovery.
Future of MPLS
While newer technologies like Software-Defined Networking (SDN) and Network Function Virtualization (NFV) are emerging, MPLS remains a relevant and widely used technology. MPLS continues to evolve, with new features and capabilities being added to address the changing needs of modern networks. In many cases, MPLS and SDN/NFV are used together to create hybrid networks that leverage the strengths of both technologies. Understanding MPLS traffic in the context of these evolving technologies is crucial for network professionals.
The future of MPLS likely involves greater integration with SDN and NFV, as well as a focus on automation and programmability. This will enable network administrators to more easily manage and optimize MPLS traffic, leading to improved network performance and agility. As networks become more complex, the need for efficient and reliable data forwarding technologies like MPLS will only continue to grow. [See also: The Evolution of Network Technologies]
Conclusion
Understanding MPLS traffic is essential for network engineers and administrators to ensure optimal network performance, reliability, and security. MPLS offers several key benefits, including improved performance, traffic engineering capabilities, QoS support, and VPN support. By implementing effective MPLS traffic engineering strategies, monitoring MPLS traffic, and securing MPLS traffic, network administrators can create a high-performance and secure network environment. While newer technologies are emerging, MPLS remains a relevant and widely used technology, and its future likely involves greater integration with SDN and NFV.