Understanding the Bazarr Default Port: Configuration and Security Best Practices
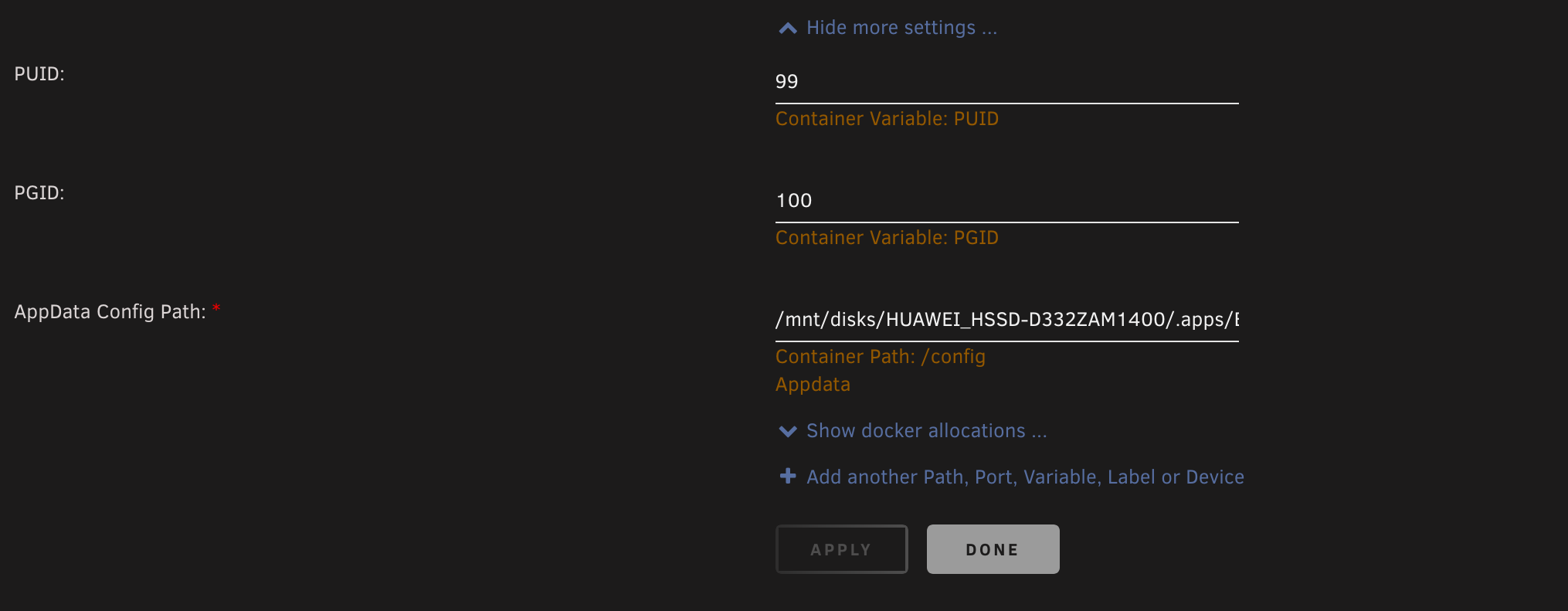
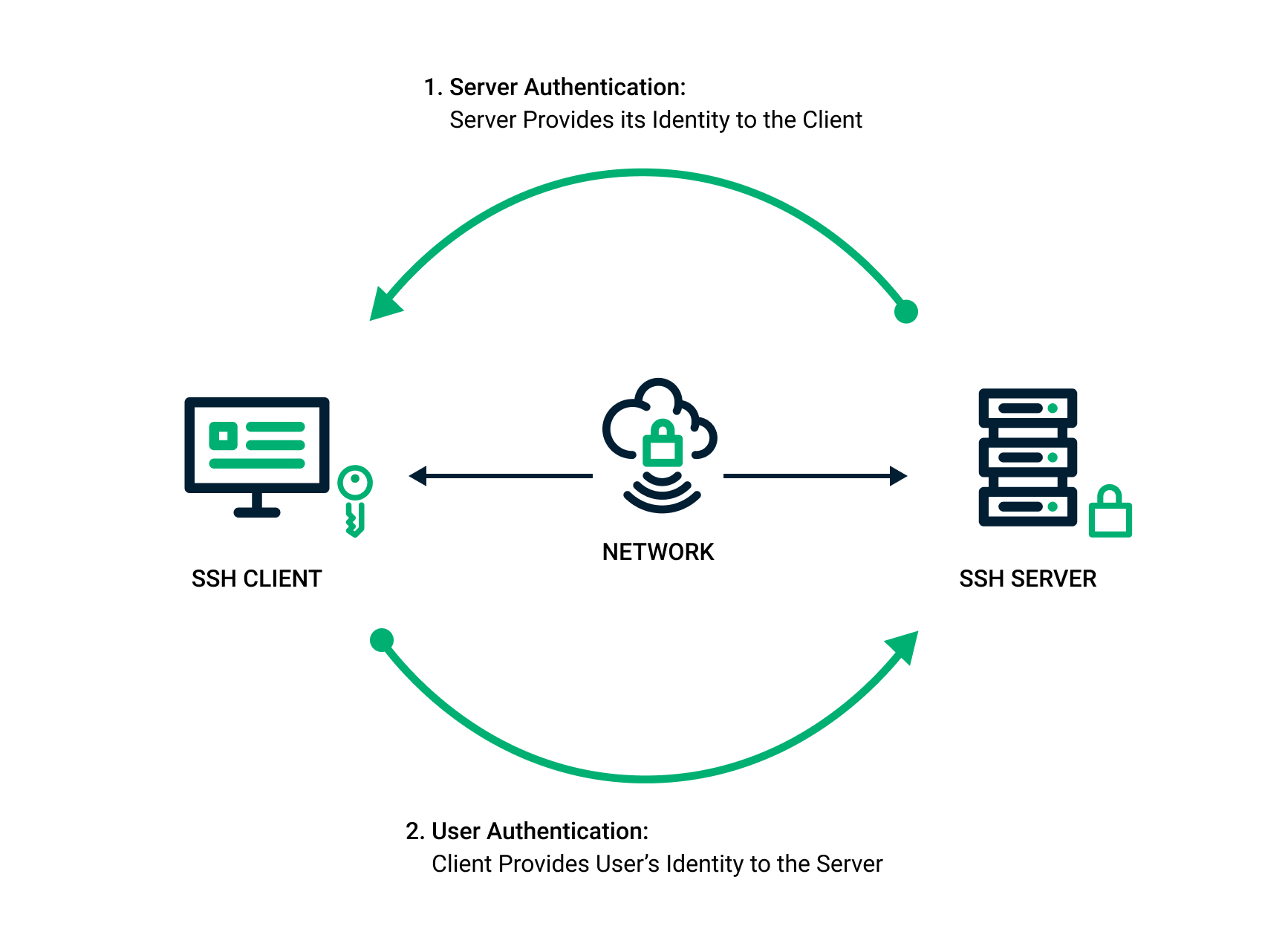
Understanding the Bazarr Default Port: Configuration and Security Best Practices Bazarr is a companion application to Sonarr and Radarr, primarily used for managing and downloading subtitles for your media library. Understanding the Bazarr default port and how it functions is crucial for setting up and securing your Bazarr instance. This article will delve into the … Read more