Securing Your Digital Fortress: Understanding SSH Private Key Permissions
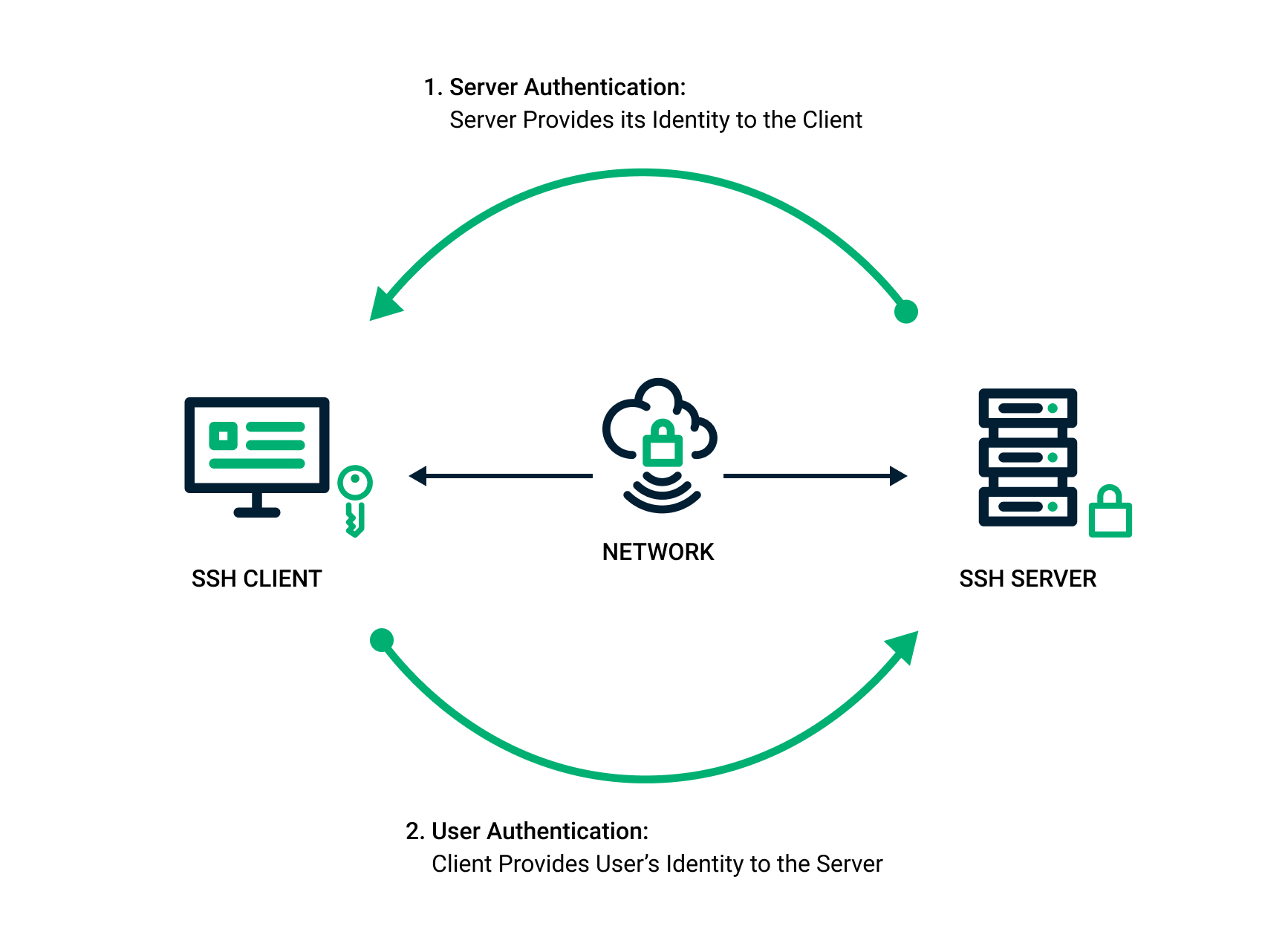
Securing Your Digital Fortress: Understanding SSH Private Key Permissions In the realm of cybersecurity, the SSH private key stands as a critical component for secure communication and access to remote systems. Think of it as the master key to your digital kingdom. However, like any valuable asset, its security hinges on proper handling and, crucially, … Read more