Config Firewall: A Comprehensive Guide to Securing Your Network
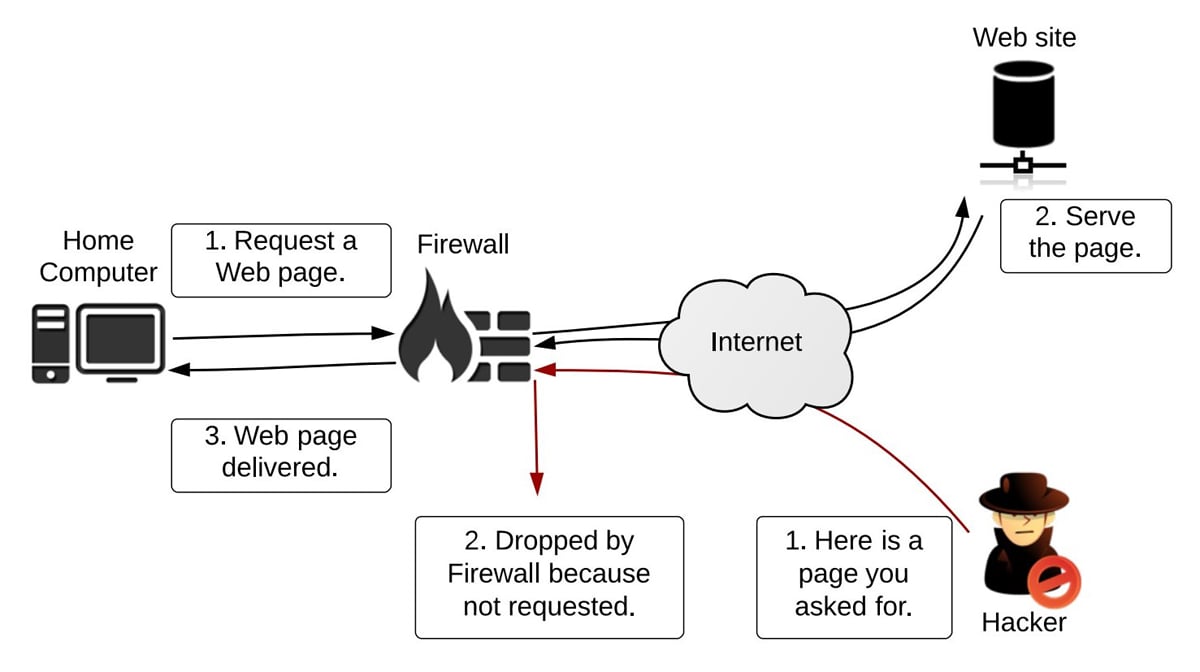
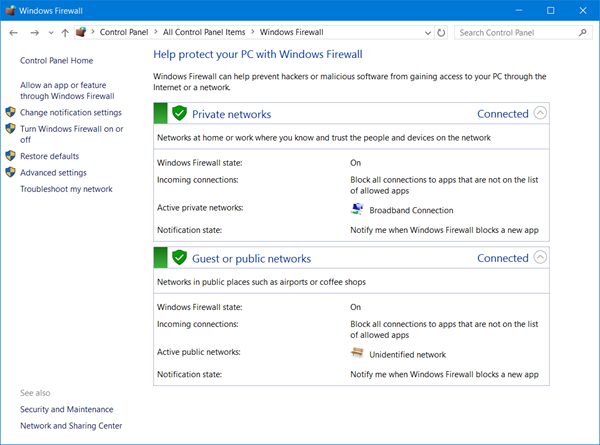
Config Firewall: A Comprehensive Guide to Securing Your Network In today’s interconnected world, network security is paramount. A firewall acts as the first line of defense, meticulously examining incoming and outgoing network traffic and blocking anything that doesn’t match the configured security policies. Understanding how to config firewall settings correctly is crucial for protecting your … Read more