Securing Your Digital Fortress: Understanding and Managing SSH Key Permissions
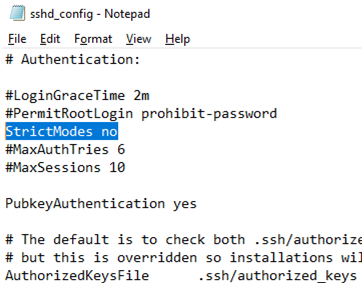
Securing Your Digital Fortress: Understanding and Managing SSH Key Permissions In the realm of cybersecurity, safeguarding sensitive data and systems is paramount. One of the most critical aspects of this endeavor is securing access to servers and other critical infrastructure. SSH, or Secure Shell, is a widely used protocol for secure remote access. While SSH … Read more