Securing Your Digital Fortress: Understanding SSH Private Key File Permissions
In the realm of cybersecurity, safeguarding your digital assets is paramount. One critical aspect of this protection involves managing your SSH (Secure Shell) private keys. These keys act as your digital identity, granting access to remote servers and systems. However, like any powerful tool, they require careful handling. In particular, understanding and implementing proper SSH private key file permissions is crucial to prevent unauthorized access and maintain the integrity of your infrastructure. This article delves into the importance of these permissions, best practices for setting them, and the potential consequences of neglecting this fundamental security measure. The security of your SSH private key file permissions is directly proportional to the overall security of your systems. Misconfigured permissions can leave you vulnerable to attack.
The Importance of SSH Private Keys
Before diving into file permissions, let’s recap why SSH private keys are so important. SSH keys provide a more secure and convenient alternative to password-based authentication. Instead of typing in a password every time you connect to a remote server, you use a private key to prove your identity. This method is significantly more resistant to brute-force attacks and password sniffing.
The core principle behind SSH key authentication lies in asymmetric cryptography. You generate a key pair: a private key and a public key. The private key, as the name suggests, should be kept secret and stored securely on your local machine. The public key is then copied to the ~/.ssh/authorized_keys file on the remote server. When you attempt to connect, the server uses the public key to verify your identity based on the private key you present. If they match, you’re granted access without needing to enter a password. Proper SSH private key file permissions ensure that only you can read your private key.
Understanding File Permissions in Linux/Unix
In Linux and Unix-like operating systems, file permissions control who can access and modify files. These permissions are represented by three categories:
- Owner: The user who owns the file.
- Group: The group associated with the file.
- Others: All other users on the system.
For each category, there are three types of permissions:
- Read (r): Allows the user to read the file’s contents.
- Write (w): Allows the user to modify the file.
- Execute (x): Allows the user to execute the file (if it’s a program).
These permissions are typically represented in two ways: symbolically (e.g., -rw-r--r--) and numerically (e.g., 644). The symbolic representation breaks down as follows:
- The first character indicates the file type (
-for regular file,dfor directory, etc.). - The next three characters represent the owner’s permissions (read, write, execute).
- The following three characters represent the group’s permissions.
- The last three characters represent the permissions for others.
The numerical representation is derived from binary values: 4 for read, 2 for write, and 1 for execute. These values are added together for each category. For example:
6(read + write)4(read only)0(no permissions)
Why Correct Permissions Matter for SSH Private Keys
Your SSH private key is a highly sensitive file. If it falls into the wrong hands, an attacker can impersonate you and gain unauthorized access to your servers. Therefore, it’s crucial to restrict access to this file as much as possible. The recommended SSH private key file permissions are 600 or -rw-------. This setting ensures that only the owner (you) can read and write the file. No one else, including members of your group or other users on the system, should have any access to it.
Consider the consequences of having overly permissive SSH private key file permissions. If the permissions are set to 644 (-rw-r--r--), anyone on the system can read your private key. An attacker could then copy the key and use it to connect to your servers as you. Similarly, if the permissions are set to 666 (-rw-rw-rw-), anyone could modify your private key, potentially injecting malicious code or replacing it with their own key.
Setting the Correct SSH Private Key File Permissions
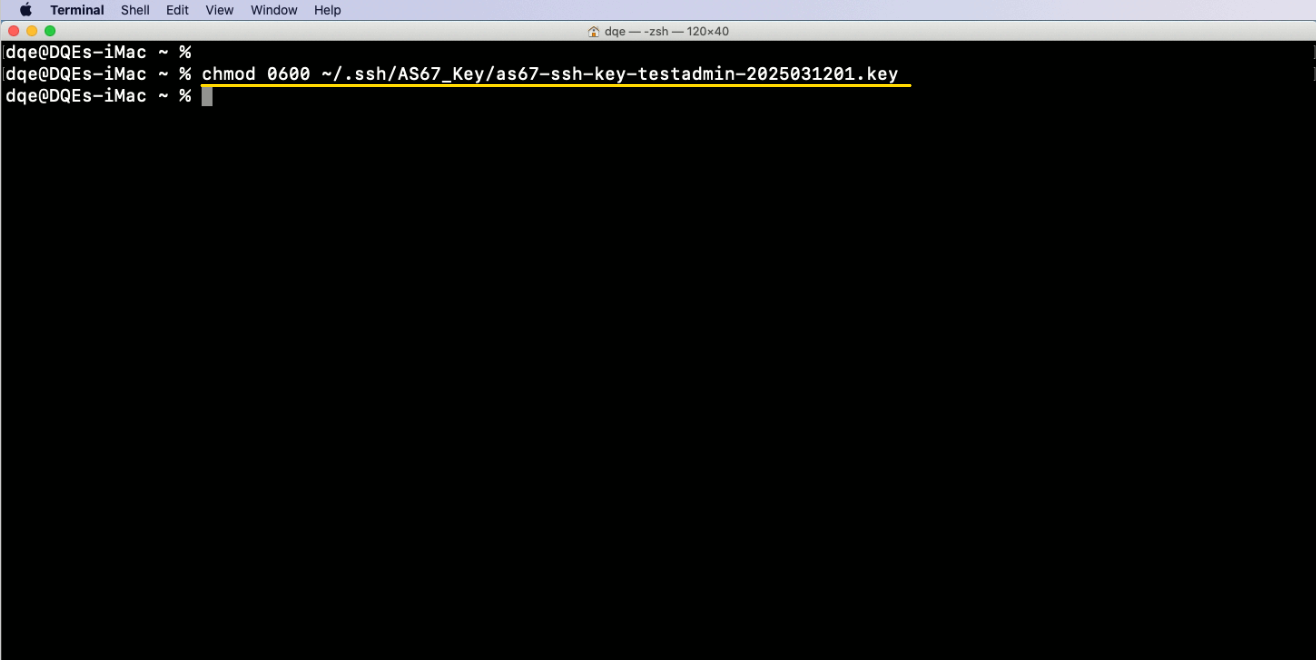
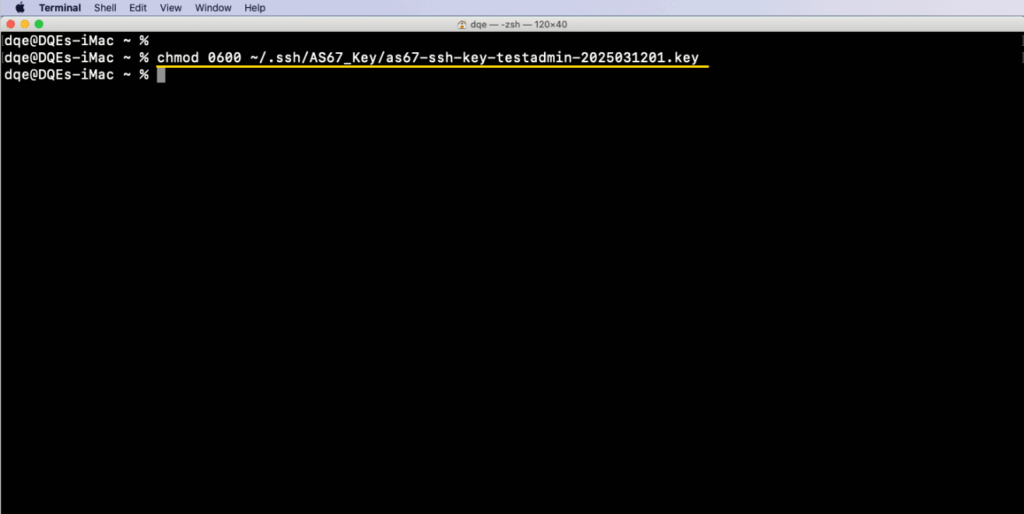
Setting the correct SSH private key file permissions is a straightforward process. You can use the chmod command in your terminal. Here’s how:
- Navigate to the directory containing your private key. Typically, this is the
~/.sshdirectory. You can use the commandcd ~/.ssh. - Identify your private key file. The default name is
id_rsa, but you might have used a different name when generating the key pair. - Set the permissions using the
chmodcommand. Run the commandchmod 600 id_rsa(replaceid_rsawith the actual name of your private key file).
To verify that the permissions have been set correctly, you can use the ls -l command. This will display the file’s permissions, owner, group, and other information. For example:
$ ls -l ~/.ssh/id_rsa
-rw------- 1 user user 1766 Oct 26 10:30 /home/user/.ssh/id_rsa
This output confirms that the owner has read and write permissions, and no one else has any access.
Checking Permissions Regularly
Setting the correct SSH private key file permissions once is not enough. It’s essential to regularly check these permissions to ensure that they haven’t been inadvertently changed. This is especially important after system updates or when working in a shared environment. You can add a regular check to your system administration scripts or use a configuration management tool to automate this process. Failing to maintain correct SSH private key file permissions can lead to unforeseen security breaches.
Dealing with Shared Environments
Shared environments, such as cloud servers or virtual machines, pose additional challenges when it comes to securing SSH private keys. In these environments, it’s crucial to ensure that only you have access to your private key file. Avoid sharing your account with others, and always use strong passwords for your user account. Additionally, consider using encryption tools to further protect your private key. This adds an extra layer of security in case your SSH private key file permissions are somehow compromised.
Beyond File Permissions: Additional Security Measures
While proper SSH private key file permissions are essential, they are just one piece of the security puzzle. Consider implementing these additional security measures to further protect your SSH keys and servers:
- Use a strong passphrase for your private key. This adds an extra layer of protection, even if your private key file is compromised.
- Disable password-based authentication. This forces users to use SSH keys, eliminating the risk of password-based attacks.
- Use multi-factor authentication (MFA). MFA adds an extra layer of security by requiring users to provide multiple forms of identification.
- Implement port knocking. This technique hides your SSH port from attackers by requiring them to send a specific sequence of packets before they can connect.
- Use a firewall. A firewall can restrict access to your SSH port, only allowing connections from trusted IP addresses.
- Regularly update your SSH server software. Security vulnerabilities are often discovered in SSH server software, so it’s important to keep it up to date.
- Monitor your SSH logs. Regularly review your SSH logs for suspicious activity, such as failed login attempts or unusual connection patterns.
The Risks of Ignoring SSH Private Key Permissions
Ignoring proper SSH private key file permissions can have serious consequences. An attacker who gains access to your private key can:
- Access your servers without your permission.
- Modify or delete your data.
- Install malware on your servers.
- Use your servers to launch attacks on other systems.
- Compromise your entire infrastructure.
The potential damage is significant, ranging from data loss and service disruption to financial losses and reputational damage. Therefore, taking the time to properly configure and maintain SSH private key file permissions is a critical investment in your organization’s security. [See also: SSH Key Management Best Practices]
Conclusion
Securing your SSH private keys is a fundamental aspect of cybersecurity. Proper SSH private key file permissions are essential to prevent unauthorized access and maintain the integrity of your systems. By understanding the importance of these permissions, following best practices for setting them, and implementing additional security measures, you can significantly reduce your risk of attack. Don’t underestimate the importance of this seemingly simple task. The security of your entire infrastructure may depend on it. Remember to regularly check your SSH private key file permissions and stay vigilant in protecting your digital assets. Protecting your SSH private key file permissions is a non-negotiable aspect of system administration. The consequences of neglecting this critical security measure can be devastating. Therefore, prioritize the security of your SSH private key file permissions and ensure that only authorized individuals have access to these sensitive files. This proactive approach will contribute significantly to the overall security posture of your organization. So, take the time to review and implement the recommendations outlined in this article. Your future self will thank you for it.