Securing Your Digital Fortress: Understanding and Managing SSH Key Permissions
In the realm of cybersecurity, safeguarding sensitive data and systems is paramount. One of the most critical aspects of this endeavor is securing access to servers and other critical infrastructure. SSH, or Secure Shell, is a widely used protocol for secure remote access. While SSH itself provides a secure channel, the security of your SSH setup heavily relies on the configuration of your SSH key permissions. Incorrect permissions can leave your systems vulnerable to unauthorized access, potentially leading to data breaches and other security incidents. This article delves into the intricacies of SSH key permissions, providing a comprehensive guide to understanding, implementing, and maintaining secure access control.
The Importance of Proper SSH Key Permissions
SSH keys offer a more secure alternative to password-based authentication. Instead of relying on easily compromised passwords, SSH keys use cryptographic key pairs: a private key that resides on your local machine and a public key that is placed on the server you wish to access. When you attempt to connect, the server verifies your identity by challenging your client to prove possession of the corresponding private key. However, the security of this system is contingent upon the protection of your private key.
If your private key falls into the wrong hands, an attacker can impersonate you and gain unauthorized access to your servers. This is where SSH key permissions come into play. Properly configured permissions ensure that only the intended user can read and use the private key, mitigating the risk of unauthorized access. Think of it like a physical key to your house; you wouldn’t want anyone to be able to pick it up and walk right in. Similarly, you need to protect your SSH key with appropriate permissions.
Understanding File Permissions in Linux/Unix
Before diving into SSH key permissions, it’s crucial to understand how file permissions work in Linux and Unix-like operating systems. These systems use a permission model based on three categories of users:
- Owner: The user who owns the file.
- Group: The group associated with the file.
- Others: All other users on the system.
For each of these categories, there are three types of permissions:
- Read (r): Allows the user to read the file’s contents.
- Write (w): Allows the user to modify the file’s contents.
- Execute (x): Allows the user to execute the file (if it’s a program) or traverse the directory (if it’s a directory).
These permissions are typically represented in a symbolic form (e.g., rwxr-xr--) or in an octal form (e.g., 755). The octal form is more commonly used when setting SSH key permissions.
The octal representation is derived from the binary representation of the permissions for each category. Read permission is represented by 4, write permission by 2, and execute permission by 1. For example, if the owner has read, write, and execute permissions, their octal value would be 4 + 2 + 1 = 7. If the group has read and execute permissions, their octal value would be 4 + 1 = 5. If others have only read permission, their octal value would be 4.
Recommended SSH Key Permissions
The recommended SSH key permissions are highly restrictive to prevent unauthorized access. Here’s a breakdown of the recommended permissions for different files and directories:
.ssh Directory
The .ssh directory in your home directory stores your SSH configuration files and keys. The recommended permissions for this directory are 700 or rwx------. This means that only the owner (you) has read, write, and execute permissions. The group and others have no permissions whatsoever.
To set these permissions, use the following command:
chmod 700 ~/.sshauthorized_keys File
The authorized_keys file within the .ssh directory stores the public keys of the users who are authorized to log in to your account. The recommended permissions for this file are 600 or rw-------. This means that only the owner (you) has read and write permissions. The group and others have no permissions.
To set these permissions, use the following command:
chmod 600 ~/.ssh/authorized_keysPrivate Key File (id_rsa)
Your private key file (e.g., id_rsa) is the most sensitive file in your SSH setup. The recommended permissions for this file are also 600 or rw-------. This ensures that only you can read and write to this file.
To set these permissions, use the following command:
chmod 600 ~/.ssh/id_rsaWhy These Permissions Are Crucial
Setting the correct SSH key permissions is not merely a suggestion; it’s a fundamental security practice. Here’s why:
- Preventing Unauthorized Access: The primary goal is to prevent unauthorized users from accessing your private key. If the permissions are too lax, other users on the system could potentially read your private key and use it to impersonate you.
- Mitigating Privilege Escalation: In some cases, vulnerabilities in system software can be exploited to gain unauthorized access to files. Restrictive SSH key permissions limit the damage that can be done even if such a vulnerability is exploited.
- Compliance Requirements: Many security standards and regulations require strict access control measures, including proper file permissions. Adhering to these standards is essential for maintaining a secure and compliant environment.
Troubleshooting SSH Key Permissions Issues
If you encounter issues connecting to a server using SSH keys, incorrect permissions are often the culprit. Here are some common error messages and how to troubleshoot them:
“WARNING: UNPROTECTED PRIVATE KEY FILE!”
This warning indicates that your private key file has permissions that are too permissive. The SSH client is warning you that your private key is vulnerable. To resolve this, set the permissions to 600 using the chmod command as described above.
“Permissions 0777 for ‘/home/user/.ssh/id_rsa’ are too open.”
This error message explicitly states that the permissions on your private key file are too open. Again, use the chmod 600 ~/.ssh/id_rsa command to correct the permissions.
Connection Refused or Authentication Failure
While not always related to permissions, connection refused or authentication failure can sometimes be caused by incorrect SSH key permissions. Double-check that the permissions on your .ssh directory, authorized_keys file, and private key file are set correctly. Also, verify that the public key in your authorized_keys file matches the public key corresponding to your private key.
Best Practices for SSH Key Management
In addition to setting the correct SSH key permissions, consider these best practices for managing your SSH keys:
- Use Strong Passphrases: While SSH keys are more secure than passwords, it’s still a good idea to protect your private key with a strong passphrase. This adds an extra layer of security in case your private key is compromised.
- Rotate Your Keys Regularly: Periodically generate new SSH keys and revoke the old ones. This limits the window of opportunity for attackers who may have compromised your keys.
- Use SSH Agent Forwarding Sparingly: SSH agent forwarding allows you to use your local private key to authenticate to other servers through an intermediate server. While convenient, this can introduce security risks. Use it only when necessary and with caution.
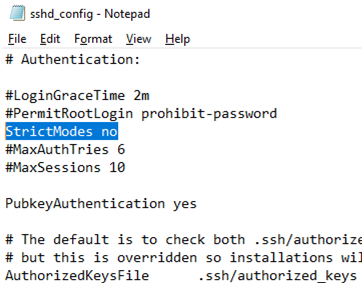
- Implement Key-Based Authentication Only: Disable password-based authentication altogether to force users to use SSH keys. This eliminates the risk of weak or compromised passwords.
- Monitor SSH Logs: Regularly review your SSH logs for suspicious activity, such as failed login attempts or unusual connection patterns.
- Store Keys Securely: If you are not using a key, store it securely, preferably offline and encrypted.
Automating SSH Key Management
Managing SSH keys across a large number of servers can be a daunting task. Fortunately, there are tools and techniques that can help automate this process:
- Configuration Management Tools: Tools like Ansible, Chef, and Puppet can be used to automate the deployment and management of SSH keys across your infrastructure.
- Centralized Key Management Systems: Solutions like HashiCorp Vault provide a centralized way to store and manage secrets, including SSH keys.
- SSH Certificate Authorities: SSH certificate authorities allow you to issue short-lived certificates that can be used to authenticate to servers, eliminating the need to manage individual SSH keys.
The Future of SSH Key Security
The landscape of cybersecurity is constantly evolving, and SSH key security is no exception. Emerging technologies and techniques are being developed to further enhance the security of SSH-based authentication:
- Hardware Security Modules (HSMs): HSMs provide a secure environment for storing and managing cryptographic keys, including SSH keys.
- Multi-Factor Authentication (MFA): Integrating MFA with SSH adds an extra layer of security by requiring users to provide multiple forms of authentication.
- Post-Quantum Cryptography: As quantum computers become more powerful, existing cryptographic algorithms may become vulnerable. Post-quantum cryptography aims to develop algorithms that are resistant to attacks from both classical and quantum computers.
Conclusion
Securing your SSH key permissions is a fundamental aspect of protecting your digital assets. By understanding the importance of proper permissions, implementing the recommended settings, and following best practices for SSH key management, you can significantly reduce the risk of unauthorized access and maintain a secure environment. Remember that cybersecurity is an ongoing process, and it’s essential to stay informed about the latest threats and vulnerabilities and adapt your security measures accordingly. Ensuring your SSH key permissions are properly configured is a crucial step in this continuous effort. Regularly review and audit your SSH key configurations to ensure they remain secure and effective. The security of your systems depends on it.
[See also: Securing SSH with Two-Factor Authentication]
[See also: Best Practices for SSH Key Rotation]
