Securing SSH: Understanding and Implementing Proper Permissions
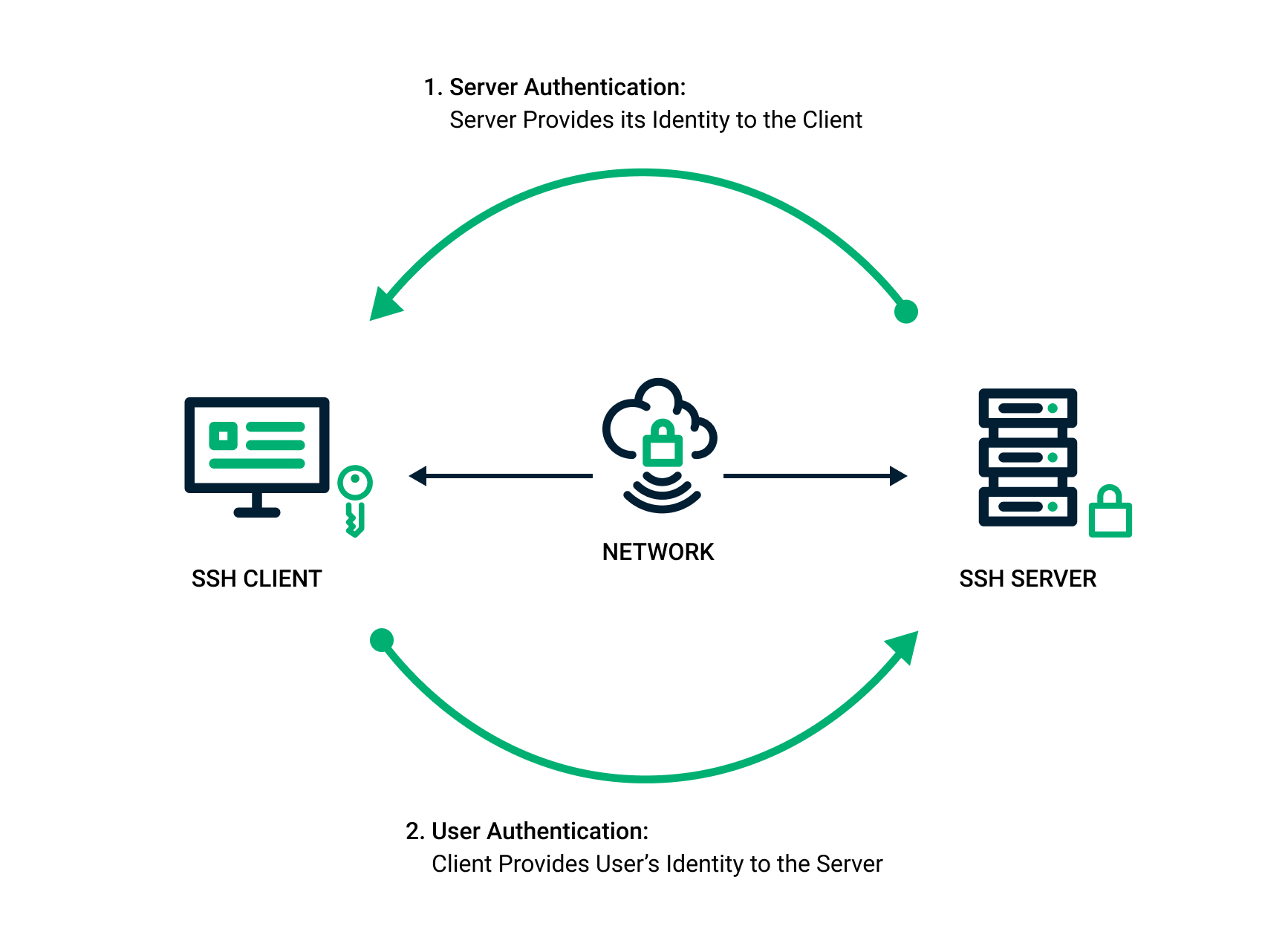
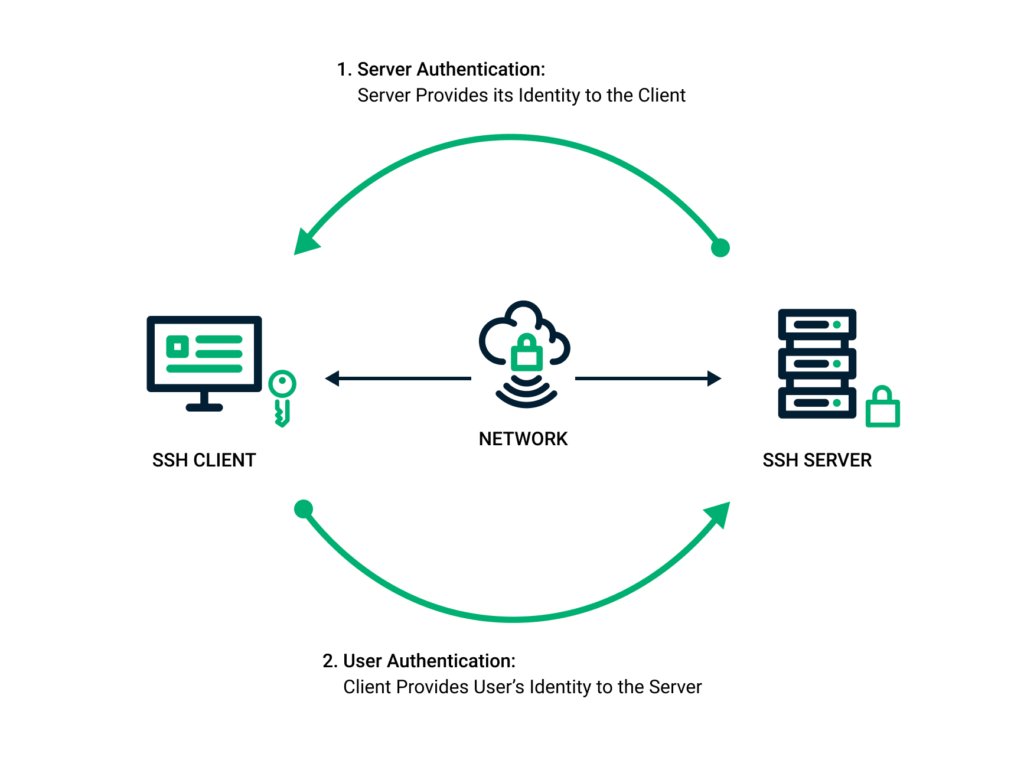
Secure Shell (SSH) is a crucial protocol for secure remote access to systems. However, its security relies heavily on proper configuration, especially concerning file and directory permissions. Incorrect SSH permissions can create vulnerabilities, allowing unauthorized access and potentially compromising the entire system. This article provides a comprehensive guide to understanding and implementing proper permissions for SSH, covering common misconfigurations, best practices, and practical examples.
The Importance of SSH Permissions
SSH uses public-key cryptography to authenticate users. This involves storing private keys on the client machine and corresponding public keys on the server. The security of this system depends on the confidentiality and integrity of these keys and associated configuration files. Weak permissions can expose these files to unauthorized users, enabling them to gain access to the system. A compromised private key, for instance, allows an attacker to impersonate the user and gain full control of their account. Therefore, implementing the correct permissions is not merely a best practice, but a fundamental security requirement.
Common SSH Permissions Issues
Several common permissions issues can weaken SSH security. These include:
- Overly Permissive Home Directories: If a user’s home directory has excessive permissions (e.g., 777), other users can potentially access and modify SSH configuration files and authorized keys.
- Weak Permissions on .ssh Directory: The
.sshdirectory, which contains authorized keys and other SSH-related files, must have strict permissions to prevent unauthorized access. - Incorrect Permissions on Authorized Keys File: The
authorized_keysfile, which lists the public keys allowed to log in to the user account, is particularly sensitive. Incorrect permissions on this file can allow unauthorized key injection. - World-Writable SSH Configuration Files: Configuration files like
/etc/ssh/sshd_configshould only be writable by the root user. World-writable configurations can be easily modified by malicious actors.
Understanding File Permissions in Linux
Before delving into specific SSH permissions, it’s essential to understand how file permissions work in Linux. Each file and directory has three types of permissions for three categories of users:
- Read (r): Allows viewing the file’s contents or listing the directory’s contents.
- Write (w): Allows modifying the file or creating/deleting files within the directory.
- Execute (x): Allows executing the file (if it’s a program) or entering the directory.
These permissions are assigned to three categories:
- User (u): The owner of the file or directory.
- Group (g): The group associated with the file or directory.
- Others (o): All other users on the system.
Permissions can be represented numerically using octal notation. Each permission (r, w, x) corresponds to a binary digit (4, 2, 1, respectively). Adding these values together creates the octal representation. For example:
rwx= 4 + 2 + 1 = 7rw-= 4 + 2 + 0 = 6r-x= 4 + 0 + 1 = 5r--= 4 + 0 + 0 = 4
Recommended SSH Permissions
The following permissions are generally recommended for SSH-related files and directories:
Home Directory
The user’s home directory should have permissions of 755 or 750. This allows the user to read, write, and execute files within their home directory, while preventing other users from modifying the contents. The command to set this is:
chmod 755 /home/username
.ssh Directory
The .ssh directory should have permissions of 700. This restricts access to the directory to only the owner. The command to set this is:
chmod 700 /home/username/.ssh
Authorized Keys File
The authorized_keys file should have permissions of 600. This ensures that only the owner can read or write to the file. The command to set this is:
chmod 600 /home/username/.ssh/authorized_keys
Private Key File
The private key file (e.g., id_rsa) should also have permissions of 600. This protects the private key from unauthorized access. The command to set this is:
chmod 600 /home/username/.ssh/id_rsa
SSH Configuration Files
The main SSH server configuration file, /etc/ssh/sshd_config, should be owned by root and have permissions of 644. This allows root to read and write the file, while other users can only read it. The command to set this is:
chmod 644 /etc/ssh/sshd_config
chown root:root /etc/ssh/sshd_config
Practical Examples
Let’s illustrate how to implement these permissions in a practical scenario. Suppose you have a user named ‘john’ and you want to ensure their SSH configuration is secure.
- Set Permissions on Home Directory:
- Set Permissions on .ssh Directory:
- Set Permissions on Authorized Keys File:
- Set Permissions on Private Key File:
chmod 755 /home/john
chmod 700 /home/john/.ssh
chmod 600 /home/john/.ssh/authorized_keys
chmod 600 /home/john/.ssh/id_rsa
After executing these commands, verify the permissions using the ls -l command. For example:
ls -ld /home/john/.ssh
ls -l /home/john/.ssh/authorized_keys
ls -l /home/john/.ssh/id_rsa
The output should confirm that the permissions are set correctly.
Automated Permissions Checks
Several tools and scripts can automate the process of checking SSH permissions. These tools can help identify misconfigurations and ensure that the system adheres to security best practices. One common approach is to use a script that iterates through user home directories and checks the permissions of SSH-related files and directories. Such scripts can be integrated into automated security audits and monitoring systems.
Troubleshooting Common Issues
Sometimes, SSH may refuse to work if the permissions are too permissive. For example, if the .ssh directory has group or world write access, SSH may refuse to use the authorized keys for authentication. In such cases, the SSH server logs will usually indicate the problem. Common error messages include:
Authentication refused: bad ownership or modes for directory /home/username/.ssh
To resolve these issues, ensure that the permissions are set as recommended above. Double-check the ownership and permissions of the .ssh directory and the authorized_keys file.
Beyond Basic Permissions: Advanced Security Measures
While correct file permissions are crucial, they are just one aspect of securing SSH. Other important security measures include:
- Disabling Password Authentication: Password authentication is vulnerable to brute-force attacks. Disabling it and relying solely on key-based authentication significantly enhances security.
- Using Strong Passphrases for Private Keys: Protecting private keys with strong passphrases adds an extra layer of security. Even if a private key is compromised, an attacker will need the passphrase to use it.
- Restricting SSH Access by IP Address: Using firewall rules or the
AllowUsersandAllowGroupsdirectives insshd_configto restrict SSH access to specific IP addresses or user groups. - Regularly Updating SSH Software: Keeping SSH software up to date ensures that security vulnerabilities are patched promptly.
- Monitoring SSH Logs: Regularly monitoring SSH logs for suspicious activity can help detect and respond to potential attacks.
Conclusion
Proper SSH permissions are a fundamental aspect of system security. By understanding the principles of file permissions in Linux and applying the recommended settings, you can significantly reduce the risk of unauthorized access to your systems. Remember to regularly review and audit your SSH configuration to ensure that it remains secure. Beyond just permissions, consider implementing other security measures like disabling password authentication and using strong passphrases. Securing SSH permissions is an ongoing process, not a one-time fix. [See also: SSH Hardening Best Practices] By staying vigilant and following best practices, you can maintain a secure SSH environment.