Config Firewall: A Comprehensive Guide to Securing Your Network
In today’s interconnected world, network security is paramount. A firewall acts as a crucial barrier, protecting your systems from unauthorized access and malicious threats. Properly configuring your firewall is essential to ensure its effectiveness. This article provides a comprehensive guide to config firewall settings, best practices, and considerations for building a robust security posture.
Understanding Firewalls
A firewall is a network security system that monitors and controls incoming and outgoing network traffic based on predetermined security rules. It acts as a gatekeeper, allowing legitimate traffic to pass while blocking potentially harmful traffic. Firewalls can be hardware-based, software-based, or a combination of both. They are a fundamental component of any network security strategy, providing a first line of defense against various cyber threats.
Types of Firewalls
- Packet Filtering Firewalls: These firewalls examine the header of each packet and compare it to a set of rules. They are relatively simple and fast but offer limited protection.
- Stateful Inspection Firewalls: These firewalls track the state of network connections, allowing them to make more informed decisions about whether to allow or block traffic. They are more secure than packet filtering firewalls.
- Proxy Firewalls: These firewalls act as intermediaries between clients and servers, hiding the internal network from the outside world. They provide a high level of security but can impact performance.
- Next-Generation Firewalls (NGFWs): These firewalls combine traditional firewall capabilities with advanced features such as intrusion prevention, application control, and malware filtering. They offer comprehensive protection against modern threats.
Key Considerations Before You Config Firewall
Before diving into the config firewall process, it’s essential to understand your network environment and security requirements. Consider the following factors:
- Network Topology: Understand the layout of your network, including the number of devices, servers, and network segments.
- Security Policies: Define clear security policies that outline acceptable use, access control, and data protection measures.
- Traffic Patterns: Analyze network traffic patterns to identify common applications, protocols, and ports used.
- Risk Assessment: Identify potential threats and vulnerabilities that could impact your network.
- Compliance Requirements: Determine if your organization is subject to any regulatory compliance requirements, such as HIPAA or PCI DSS.
Steps to Config Firewall Effectively
Configuring a firewall involves a series of steps, each crucial for ensuring optimal security. Here’s a detailed breakdown:
Step 1: Initial Setup and Configuration
Begin by accessing the firewall’s management interface, typically through a web browser or command-line interface. Change the default administrator password immediately to prevent unauthorized access. Configure basic network settings, such as IP address, subnet mask, and gateway.
Step 2: Defining Firewall Rules
Firewall rules are the foundation of your security policy. Each rule specifies criteria for allowing or blocking network traffic. Rules are typically based on the following parameters:
- Source IP Address: The IP address of the device sending the traffic.
- Destination IP Address: The IP address of the device receiving the traffic.
- Source Port: The port number used by the sending application.
- Destination Port: The port number used by the receiving application.
- Protocol: The network protocol used, such as TCP, UDP, or ICMP.
- Action: The action to take, such as allow, deny, or reject.
When you config firewall rules, a general best practice is to follow the principle of least privilege, granting only the minimum necessary access. Start with a default deny policy, blocking all traffic by default, and then create rules to allow specific traffic that is required for legitimate business purposes.
Step 3: Configuring Network Address Translation (NAT)
NAT allows you to translate private IP addresses within your internal network to a single public IP address when communicating with the internet. This provides an additional layer of security by hiding the internal network structure from the outside world. Config firewall to perform NAT is often essential for protecting internal resources.
Step 4: Setting Up Intrusion Prevention System (IPS)
Many modern firewalls include an integrated IPS, which monitors network traffic for malicious activity and automatically blocks or mitigates threats. Config firewall IPS settings to detect and prevent common attacks, such as buffer overflows, SQL injection, and cross-site scripting.
Step 5: Enabling Logging and Monitoring
Logging and monitoring are crucial for identifying and responding to security incidents. Config firewall to log all network traffic, including allowed and blocked connections. Regularly review the logs to identify suspicious activity and potential security breaches. Consider using a Security Information and Event Management (SIEM) system to aggregate and analyze logs from multiple sources.
Step 6: Regular Updates and Maintenance
Firewall software and firmware should be updated regularly to patch security vulnerabilities and improve performance. Subscribe to security advisories from your firewall vendor to stay informed about the latest threats and vulnerabilities. Regularly review and update your firewall rules to ensure they are still relevant and effective. Proactive config firewall maintenance is key to long-term security.
Best Practices for Firewall Configuration
Following best practices can significantly enhance your firewall’s effectiveness:
- Use Strong Passwords: Use strong, unique passwords for all firewall accounts.
- Enable Multi-Factor Authentication (MFA): Enable MFA for administrator accounts to add an extra layer of security.
- Disable Unnecessary Services: Disable any unnecessary services or features to reduce the attack surface.
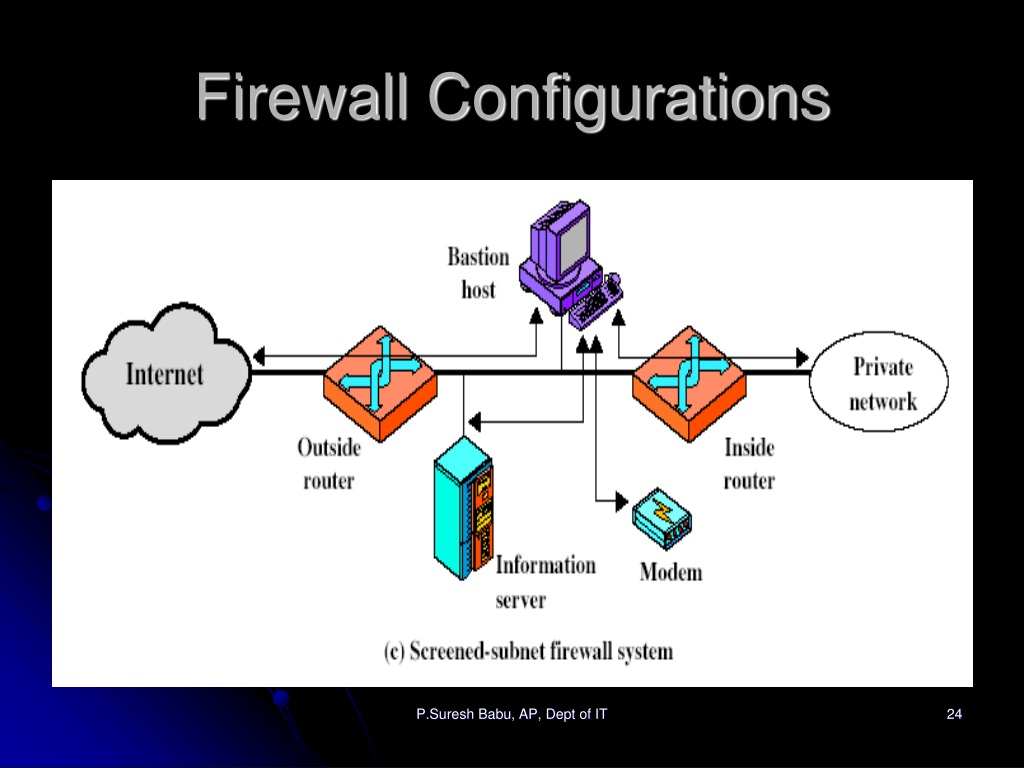
- Segment Your Network: Segment your network into smaller, isolated segments to limit the impact of a security breach.
- Implement a DMZ: Create a Demilitarized Zone (DMZ) for hosting public-facing servers, such as web servers and email servers.
- Regularly Test Your Firewall: Conduct regular penetration testing to identify vulnerabilities in your firewall configuration.
- Document Your Configuration: Document your firewall configuration, including all rules and settings, to facilitate troubleshooting and maintenance.
Troubleshooting Common Firewall Issues
Even with careful planning and configuration, you may encounter issues with your firewall. Here are some common problems and their solutions:
- Blocked Traffic: If legitimate traffic is being blocked, review your firewall rules to ensure that the necessary ports and protocols are allowed.
- Performance Issues: If your firewall is causing performance issues, consider optimizing your rules or upgrading to a more powerful firewall.
- Connectivity Problems: If you are experiencing connectivity problems, check your firewall logs to see if any traffic is being blocked.
- Configuration Errors: If you are unsure about a particular configuration setting, consult your firewall vendor’s documentation or seek assistance from a qualified security professional.
The Future of Firewalls
Firewall technology is constantly evolving to meet the ever-changing threat landscape. Cloud-based firewalls, also known as Firewall-as-a-Service (FWaaS), are becoming increasingly popular, offering scalability, flexibility, and centralized management. Artificial intelligence (AI) and machine learning (ML) are also being integrated into firewalls to automate threat detection and response. As threats become more sophisticated, the ability to effectively config firewall solutions will become even more critical.
Conclusion
Configuring a firewall is a critical step in securing your network. By following the guidelines and best practices outlined in this article, you can build a robust security posture and protect your systems from unauthorized access and malicious threats. Remember that firewall configuration is an ongoing process that requires regular review and maintenance. Prioritize understanding your network’s specific needs and tailoring your firewall configuration to meet those needs. Don’t underestimate the importance of proper config firewall practices; it’s a cornerstone of modern network security. [See also: Network Security Best Practices] [See also: Choosing the Right Firewall] [See also: Understanding Intrusion Detection Systems]
