Config Firewall: A Comprehensive Guide to Securing Your Network
In today’s interconnected world, network security is paramount. A firewall acts as the first line of defense against unauthorized access and malicious attacks. Properly configuring your config firewall is crucial for protecting sensitive data and ensuring the continuity of your business operations. This comprehensive guide will delve into the essential aspects of config firewall, covering its importance, key configuration steps, and best practices.
Understanding the Importance of Firewall Configuration
A firewall, in essence, is a network security system that monitors and controls incoming and outgoing network traffic based on predetermined security rules. Think of it as a gatekeeper for your network, deciding which traffic is allowed to pass through and which is blocked. Without a properly config firewall, your network is vulnerable to a wide range of threats, including:
- Malware Infections: Viruses, worms, and Trojans can infiltrate your network and compromise your systems.
- Data Breaches: Sensitive information, such as customer data and financial records, can be stolen or leaked.
- Denial-of-Service (DoS) Attacks: Attackers can flood your network with traffic, making it unavailable to legitimate users.
- Unauthorized Access: Hackers can gain access to your systems and steal data or disrupt operations.
A well-config firewall mitigates these risks by creating a barrier between your internal network and the outside world. It examines network traffic and blocks any traffic that doesn’t meet your defined security policies. This proactive approach significantly reduces the likelihood of a successful attack.
Key Configuration Steps for Your Config Firewall
Configuring a firewall involves several critical steps. The specific steps may vary depending on the type of firewall you’re using (hardware or software) and the vendor, but the following are some general guidelines:
Initial Setup and Basic Configuration
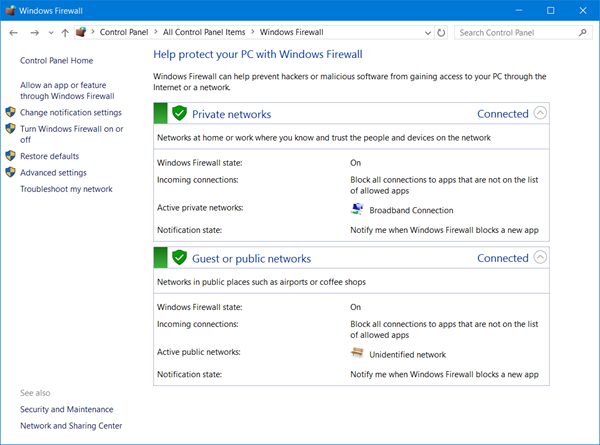
The first step is to install and set up your firewall. This typically involves connecting the firewall to your network and configuring its basic settings, such as its IP address and hostname. You’ll also need to set up administrative access and configure logging.
Defining Network Zones
Network zones are logical groupings of network segments based on their security levels. Common zones include:
- Internal Network: Your trusted network where your servers and workstations reside.
- External Network (WAN): The public internet.
- DMZ (Demilitarized Zone): A buffer zone between your internal network and the external network, typically used for hosting public-facing servers.
By defining these zones, you can create more granular security policies and control traffic flow between them. Make sure your config firewall is configured to properly separate these zones.
Creating Firewall Rules
Firewall rules are the core of your config firewall. They define which traffic is allowed or blocked based on various criteria, such as:
- Source IP Address: The IP address of the device sending the traffic.
- Destination IP Address: The IP address of the device receiving the traffic.
- Source Port: The port number of the application sending the traffic.
- Destination Port: The port number of the application receiving the traffic.
- Protocol: The network protocol being used (e.g., TCP, UDP).
When creating firewall rules, it’s essential to follow the principle of least privilege, which means granting only the minimum necessary access. Start by blocking all traffic by default and then create rules to allow specific traffic as needed. For example, you might create a rule to allow HTTP traffic (port 80) to your web server in the DMZ.
Configuring Intrusion Detection and Prevention Systems (IDS/IPS)
Many modern firewalls include IDS/IPS capabilities, which can detect and prevent malicious activity in real-time. IDS monitors network traffic for suspicious patterns and alerts administrators, while IPS actively blocks or mitigates threats. Configuring IDS/IPS involves defining rules and signatures to identify known attacks and vulnerabilities. A properly config firewall with IDS/IPS can significantly enhance your network security posture.
Enabling Logging and Monitoring
Logging and monitoring are crucial for identifying and responding to security incidents. Your config firewall should be configured to log all network traffic, including allowed and blocked connections. These logs can be analyzed to identify suspicious activity, troubleshoot network problems, and demonstrate compliance with security regulations. Consider using a Security Information and Event Management (SIEM) system to centralize and analyze your firewall logs.
Best Practices for Firewall Configuration
In addition to the basic configuration steps, following these best practices will help you maximize the effectiveness of your config firewall:
Regularly Update Your Firewall Firmware
Firewall vendors regularly release firmware updates to address security vulnerabilities and improve performance. It’s essential to install these updates promptly to protect your network from known threats. Schedule regular maintenance windows to apply firmware updates and test the functionality of your firewall.
Implement Strong Password Policies
Protect your firewall’s administrative access with strong passwords and multi-factor authentication. Use a password manager to generate and store complex passwords. Regularly review and update your password policies to ensure they meet current security standards.
Conduct Regular Security Audits
Regularly audit your firewall configuration to identify potential weaknesses and ensure that your security policies are up-to-date. Use vulnerability scanners to identify known vulnerabilities in your firewall and other network devices. Consider hiring a third-party security firm to conduct a comprehensive security assessment.
Monitor Network Traffic for Suspicious Activity
Continuously monitor your network traffic for suspicious activity, such as unusual traffic patterns, unauthorized access attempts, and malware infections. Use intrusion detection systems (IDS) and security information and event management (SIEM) systems to automate this process. Respond promptly to any security alerts and investigate potential incidents thoroughly.
Document Your Firewall Configuration
Maintain detailed documentation of your firewall configuration, including network diagrams, firewall rules, and security policies. This documentation will be invaluable for troubleshooting problems, making changes to your configuration, and training new administrators. Keep your documentation up-to-date and readily accessible.
Test Your Firewall Configuration
Regularly test your firewall configuration to ensure that it is working as expected. Use penetration testing tools to simulate real-world attacks and identify potential weaknesses in your security posture. Conduct these tests in a controlled environment to avoid disrupting your production network.
Advanced Firewall Configuration Techniques
Beyond the basics, several advanced techniques can further enhance your firewall security. These include:
Stateful Packet Inspection (SPI)
SPI firewalls track the state of network connections and only allow traffic that is part of an established connection. This helps prevent spoofing and other types of attacks. Ensure your config firewall leverages SPI for enhanced security.
Application-Layer Filtering
Application-layer filtering allows you to control traffic based on the application being used, rather than just the port number. This can help prevent malware from using legitimate ports to bypass your firewall. Many modern firewalls offer application-layer filtering capabilities.
Virtual Private Networks (VPNs)
VPNs create secure connections between your network and remote users or other networks. Firewalls can be used to terminate VPN connections and enforce security policies on VPN traffic. A config firewall can be a key component of your VPN infrastructure.
Web Application Firewalls (WAFs)
WAFs are specialized firewalls that protect web applications from attacks such as SQL injection and cross-site scripting (XSS). If you host web applications, consider deploying a WAF in addition to your traditional firewall. WAFs offer an additional layer of security specifically tailored to web applications.
Choosing the Right Firewall for Your Needs
Selecting the right firewall is a critical decision. Consider these factors:
- Network Size and Complexity: Larger and more complex networks require more powerful and feature-rich firewalls.
- Security Requirements: Evaluate your specific security needs and choose a firewall that offers the features and capabilities you require.
- Budget: Firewalls range in price from free software firewalls to expensive hardware appliances. Choose a firewall that fits your budget and meets your needs.
- Ease of Use: Select a firewall that is easy to configure and manage.
- Vendor Reputation: Choose a firewall from a reputable vendor with a proven track record of security and reliability.
Conclusion
Configuring your firewall effectively is essential for protecting your network from cyber threats. By following the steps and best practices outlined in this guide, you can create a strong security perimeter and minimize your risk of attack. Remember to regularly update your firewall, monitor network traffic, and conduct security audits to ensure that your firewall remains effective. A well-config firewall is a cornerstone of any robust security strategy. Don’t underestimate the importance of proper config firewall practices; they can save you time, money, and reputation in the long run. Always prioritize network security and take proactive measures to protect your valuable data. The config firewall is your primary defense, so treat it as such and ensure its optimal performance. Regular maintenance and updates to your config firewall are also key. A properly configured config firewall significantly reduces your risk. Remember that a default config firewall is rarely sufficient. Tailor your config firewall to your specific needs. Security professionals emphasize the importance of a strong config firewall strategy. Finally, continuously improve your config firewall based on new threats and vulnerabilities. A well managed config firewall is an essential component of a secure network. Understanding and properly implementing a config firewall is paramount for any organization. Securing your network begins with a strong config firewall.
[See also: Understanding Network Security]
[See also: Best Practices for Cybersecurity]
[See also: Choosing the Right Firewall Solution]
