Understanding P2P Systems: A Comprehensive Overview
Peer-to-peer (P2P) systems have revolutionized various aspects of digital interaction, from file sharing to cryptocurrency networks. This article provides a comprehensive overview of P2P systems, exploring their architecture, applications, advantages, disadvantages, and future trends. Understanding P2P networks is crucial in today’s interconnected world, as they underpin many technologies we use daily. Let’s delve into the intricacies of P2P technology.
What are P2P Systems?
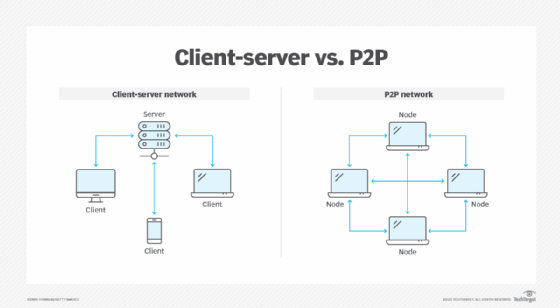
At its core, a P2P system is a decentralized network architecture where each participant, or “peer,” has equal capabilities and responsibilities. Unlike traditional client-server models, where a central server provides resources and services to clients, P2P networks allow peers to directly share resources with each other. This distributed nature eliminates the need for a central authority, making P2P systems inherently more resilient and scalable.
Key Characteristics of P2P Networks
- Decentralization: No central server controls the network.
- Peer Equality: All nodes have similar capabilities and responsibilities.
- Resource Sharing: Peers share resources such as files, processing power, and bandwidth.
- Scalability: The network can easily grow without significant performance degradation.
- Resilience: Failure of individual nodes does not disrupt the entire network.
Architecture of P2P Networks
The architecture of P2P networks can vary, but the most common types include:
Unstructured P2P Networks
In unstructured P2P networks, peers are connected randomly. This simplicity makes them easy to build and maintain. However, searching for content can be inefficient, often relying on flooding the network with queries. Examples include early versions of Napster and Gnutella.
Structured P2P Networks
Structured P2P networks impose a specific organization on the network topology, typically using distributed hash tables (DHTs) to map resources to specific peers. This structure allows for more efficient searching and retrieval of content. Examples include Chord and CAN.
Hybrid P2P Networks
Hybrid P2P networks combine elements of both centralized and decentralized architectures. They often use a central server for indexing and discovery, while the actual file transfer occurs directly between peers. This approach balances the benefits of both models. A prime example is the original Napster, which used a central server for indexing but allowed users to download files directly from each other.
Applications of P2P Systems
P2P systems have found applications in various domains, including:
File Sharing
One of the earliest and most well-known applications of P2P technology is file sharing. Platforms like BitTorrent allow users to download large files quickly and efficiently by distributing the download across multiple peers. [See also: Best Practices for Secure File Sharing]
Cryptocurrencies
Cryptocurrencies like Bitcoin rely on P2P networks to maintain a decentralized and secure ledger of transactions. The blockchain is distributed across multiple nodes, ensuring transparency and preventing single points of failure.
Content Delivery Networks (CDNs)
P2P CDNs distribute content across multiple nodes, reducing the load on central servers and improving delivery speeds. This is particularly useful for streaming video and other bandwidth-intensive applications.
Collaborative Applications
P2P networks can facilitate collaborative applications by allowing users to share resources and communicate directly with each other. Examples include collaborative editing tools and distributed computing projects.
Voice over IP (VoIP)
Some VoIP applications use P2P technology to establish direct connections between users, reducing latency and improving call quality. Skype, in its early days, utilized P2P for call routing.
Advantages of P2P Systems
P2P systems offer several advantages over traditional client-server models:
Scalability
P2P networks can scale easily as new peers join the network, increasing the overall capacity and performance. Each new peer contributes resources, rather than straining a central server.
Resilience
The decentralized nature of P2P systems makes them highly resilient to failures. If one peer goes offline, the network can continue to function without interruption. This is because other peers can take over the responsibilities of the failed node.
Cost-Effectiveness
By distributing resources across multiple peers, P2P networks can reduce the need for expensive central servers, leading to significant cost savings. This is particularly beneficial for applications with high bandwidth requirements.
Anonymity and Privacy
Some P2P networks offer enhanced anonymity and privacy by routing traffic through multiple peers, making it difficult to trace the origin or destination of data. This is a key feature for applications that require a high level of privacy, such as secure messaging and anonymous file sharing.
Disadvantages of P2P Systems
Despite their advantages, P2P systems also have some drawbacks:
Security Risks
The decentralized nature of P2P networks can make them vulnerable to security threats, such as malware distribution and denial-of-service attacks. It’s crucial to implement robust security measures to protect against these risks.
Copyright Infringement
P2P networks have been associated with copyright infringement due to the ease with which users can share copyrighted material. This has led to legal challenges and efforts to regulate P2P file sharing.
Quality of Service
The quality of service in P2P networks can vary depending on the availability and performance of individual peers. This can result in inconsistent download speeds and unreliable connections.
Complexity
Designing and implementing P2P systems can be complex, particularly when dealing with issues such as routing, security, and resource management. This requires specialized expertise and careful planning.
Future Trends in P2P Systems
The future of P2P systems looks promising, with several emerging trends shaping their evolution:
Blockchain Integration
The integration of blockchain technology with P2P networks is enabling new applications in areas such as decentralized finance (DeFi) and supply chain management. This combination offers enhanced security, transparency, and efficiency.
Edge Computing
P2P principles are being applied in edge computing to distribute processing and storage closer to the source of data. This reduces latency and improves performance for applications such as IoT and autonomous vehicles. [See also: The Convergence of Edge Computing and P2P Networks]
Decentralized Applications (DApps)
P2P networks are the foundation for many decentralized applications (DApps) that offer alternatives to traditional centralized services. These DApps span various domains, including social media, gaming, and finance.
Improved Security Measures
Ongoing research and development are focused on improving the security of P2P systems through techniques such as encryption, authentication, and intrusion detection. This is essential for addressing the security risks associated with decentralized networks.
Conclusion
P2P systems represent a powerful paradigm for distributed computing and resource sharing. While they offer numerous advantages, such as scalability, resilience, and cost-effectiveness, they also present challenges related to security and copyright infringement. As technology evolves, P2P networks are expected to play an increasingly important role in various applications, from file sharing and cryptocurrencies to content delivery and decentralized applications. Understanding the principles and characteristics of P2P systems is essential for anyone involved in the development and deployment of modern distributed technologies. The future of P2P is bright, with ongoing innovations promising to unlock even greater potential and address existing limitations. The key to successful P2P implementation lies in carefully considering the specific requirements of the application and implementing appropriate security and management measures. With the right approach, P2P systems can provide a robust and efficient solution for a wide range of use cases.
