Understanding and Correcting .ssh Folder Permissions: A Comprehensive Guide
Secure Shell (SSH) is a critical protocol for secure remote access to systems. Proper configuration, especially concerning .ssh folder permissions, is paramount for maintaining system security. Incorrect permissions can expose your system to unauthorized access. This guide provides a comprehensive understanding of .ssh folder permissions, why they matter, and how to correctly configure them.
Why .ssh Folder Permissions Matter
The .ssh directory, located in a user’s home directory (e.g., /home/user/.ssh), stores sensitive information such as private keys, authorized keys, and known hosts. These files are essential for passwordless authentication and secure communication. If the permissions on the .ssh folder or its contents are too permissive, an attacker could potentially gain unauthorized access to your system.
Specifically, if other users on the system can read or write to your .ssh directory or its files, they might be able to:
- Steal your private key: A stolen private key allows an attacker to impersonate you and access remote servers without your knowledge.
- Modify your authorized_keys file: An attacker could add their public key to your authorized_keys file, granting them persistent access to your account.
- Compromise your system: Once an attacker has access, they can install malware, steal data, or use your system as a launchpad for further attacks.
Default and Recommended Permissions
The recommended permissions for the .ssh directory and its files are as follows:
- .ssh directory:
700(drwx------) – Only the owner has read, write, and execute permissions. Group and others have no permissions. - authorized_keys file:
600(-rw-------) – Only the owner has read and write permissions. Group and others have no permissions. - id_rsa (private key) file:
600(-rw-------) – Only the owner has read and write permissions. Group and others have no permissions. - id_rsa.pub (public key) file:
644(-rw-r--r--) – The owner has read and write permissions, and the group and others have read-only permissions. While not strictly required, this is generally safe as the public key is meant to be shared. - known_hosts file:
600or644(-rw-------or-rw-r--r--) – The owner has read and write permissions, and optionally, the group and others have read-only permissions.
Checking .ssh Folder Permissions
You can check the permissions of your .ssh directory and its files using the ls -l command in your terminal. Open your terminal and navigate to your home directory:
cd ~Then, list the contents of the .ssh directory with detailed information:
ls -l .sshThe output will display the permissions, owner, group, and modification date for each file in the directory. For example:
drwx------ 2 user user 4096 Oct 26 10:00 .ssh
-rw------- 1 user user 524 Oct 26 10:00 authorized_keys
-rw------- 1 user user 1675 Oct 26 10:00 id_rsa
-rw-r--r-- 1 user user 401 Oct 26 10:00 id_rsa.pub
-rw------- 1 user user 358 Oct 26 10:00 known_hostsIn this example, the .ssh directory has the correct permissions (drwx------), and the authorized_keys, id_rsa, and known_hosts files also have the recommended permissions (-rw-------). The id_rsa.pub file has permissions -rw-r--r--, which is also acceptable.
Correcting Incorrect .ssh Folder Permissions
If you find that your .ssh folder permissions are incorrect, you can correct them using the chmod command. The chmod command allows you to change the permissions of files and directories.
Correcting .ssh Directory Permissions
To set the correct permissions for the .ssh directory, use the following command:
chmod 700 .sshThis command sets the permissions of the .ssh directory to 700, which means that only the owner (you) has read, write, and execute permissions.
Correcting authorized_keys File Permissions
To set the correct permissions for the authorized_keys file, use the following command:
chmod 600 .ssh/authorized_keysThis command sets the permissions of the authorized_keys file to 600, which means that only the owner (you) has read and write permissions.
Correcting id_rsa (Private Key) File Permissions
To set the correct permissions for the id_rsa (private key) file, use the following command:
chmod 600 .ssh/id_rsaThis command sets the permissions of the id_rsa file to 600, which means that only the owner (you) has read and write permissions. It’s crucial that your private key is not readable by others.
Correcting id_rsa.pub (Public Key) File Permissions
While not strictly necessary, you can set the permissions for the id_rsa.pub (public key) file to 644 using the following command:
chmod 644 .ssh/id_rsa.pubCorrecting known_hosts File Permissions
To set the correct permissions for the known_hosts file, use the following command:
chmod 600 .ssh/known_hostsOr, if you prefer, you can use:
chmod 644 .ssh/known_hostsPotential Issues and Troubleshooting
If you encounter issues after changing the .ssh folder permissions, such as being unable to log in via SSH, double-check the permissions to ensure they are set correctly. Also, verify that the owner of the .ssh directory and its files is the correct user.
You can check the owner using the ls -l command. The output will show the owner and group for each file. If the owner is incorrect, you can change it using the chown command. For example, to change the owner of the .ssh directory to the user ‘john’, use the following command:
sudo chown john:john .sshReplace ‘john’ with the actual username. Also, ensure that the group is set correctly. Incorrect ownership can prevent SSH from working correctly, even if the permissions are right.
Security Best Practices
In addition to setting the correct .ssh folder permissions, consider the following security best practices:
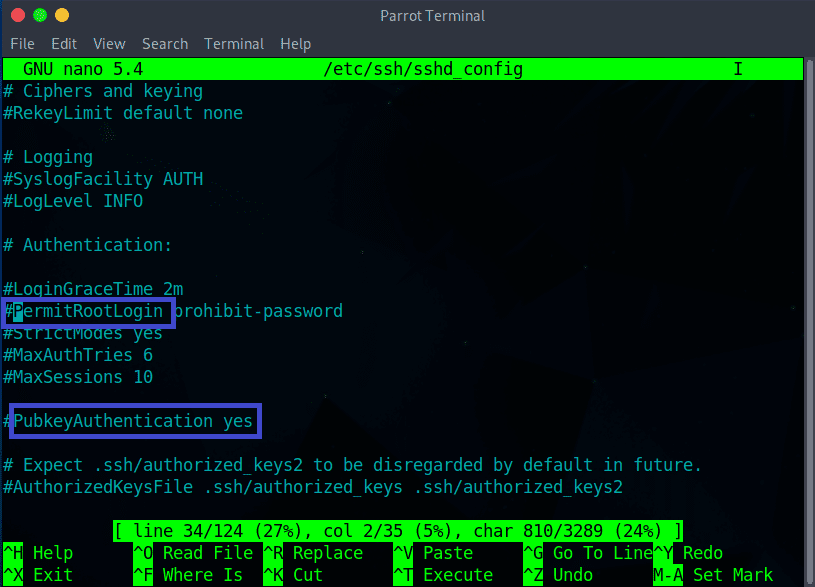
- Disable password authentication: Password authentication is less secure than key-based authentication. Disable it in your SSH server configuration file (
/etc/ssh/sshd_config) by settingPasswordAuthentication no. - Use strong passphrases for your private keys: A strong passphrase adds an extra layer of security to your private key.
- Regularly rotate your SSH keys: Periodically generate new SSH keys and revoke the old ones.
- Monitor SSH logs: Regularly review your SSH logs for suspicious activity.
- Use a firewall: Configure a firewall to restrict access to your SSH port (default is 22) to only trusted IP addresses.
Automating .ssh Permission Checks
To ensure ongoing security, consider automating checks for correct .ssh folder permissions. You can use scripting tools like Bash or Python to periodically verify the permissions and alert you if any deviations are detected. This proactive approach can help you quickly identify and address potential security vulnerabilities.
Conclusion
Correct .ssh folder permissions are essential for maintaining the security of your systems. By understanding the recommended permissions and following the steps outlined in this guide, you can protect your systems from unauthorized access and ensure secure remote communication. Regularly review and automate checks for these permissions to maintain a strong security posture. Remember to always prioritize security best practices when configuring SSH.
By implementing these measures, you can significantly reduce the risk of SSH-related security breaches and maintain a secure computing environment.
[See also: SSH Key Management Best Practices]
[See also: Securing Your Linux Server]
